Before he was charged in July 2011 with aiding the hacker group Anonymous, Josh Covelli lived what he considered the life of an ordinary 26-year-old. He spent countless hours on the Internet. He had a girlfriend. He was a student and employee at Devry University in Dayton, Ohio.
But after federal authorities accused him and 13 other people of helping launch a cyberattack against the online payment service PayPal, Covelli faced potentially 15 years in prison, and his life began to unravel.
His girlfriend broke up with him. He struggled to find an employer willing to hire an accused computer hacker. His friends "wanted nothing to do with me," he said, and he suffered from bouts of paranoia -- "looking out windows, not sure who to trust" -- before checking into a behavioral health center for three days.
"It was as if I got kicked off a cliff," Covelli, now 28, told The Huffington Post in an interview.
Nearly two years after the charges made headlines, the case remains an anxiety-provoking daily reality for Covelli and his 13 co-defendants. Though they come from disparate worlds -- drawn from different points on the map and stages in their lives -- the defendants collectively share a sense of unsettling uncertainty, their plans and aspirations stuck in a limbo of indeterminate duration as they await a resolution of their case.
Their wait may be nearing a conclusion. This week, the defendants -- known collectively as the "PayPal 14" -- attended a closed-door hearing in federal court in San Francisco in hopes of negotiating a settlement that could keep them out of prison. Lawyers for both sides declined to discuss the negotiations, but a joint court filing called the meeting "productive."
"We're at a delicate point," one defense attorney said in an interview.
Such a deal would mark the final chapter in a case that has been seen as one of the first major salvos in the federal government's war on Anonymous, a loose collective of hackers who say they are motivated by ideological beliefs, not financial gain. It would also bring to a close months of legal uncertainty that the defendants say has caused them both financial and emotional strain. One defendant in the case told The Huffington Post that she would "jump off the Hoover Dam" if convicted.
While the PayPal case has largely faded from public view, the law under which the 14 defendants were charged -- the Computer Fraud and Abuse Act -- has come under increased scrutiny. The government used the same anti-hacking law to prosecute Internet activist Aaron Swartz, charging him with illegally downloading millions of articles from a Massachusetts Institute of Technology computer archive. Facing the prospect of a lengthy prison sentence, Swartz committed suicide, provoking claims of prosecutorial overreach and calls to reform the law. Critics say it is overly broad and excessively punitive, meting out stiff prison terms for some computer-related crimes they deem relatively innocuous.
The PayPal arrests appeared to have done little to deter Anonymous. Six months after the indictment was unsealed, in January 2012, Anonymous launched one of its largest attacks, knocking offline the Justice Department's website in protest of the U.S. government's arrest of leaders of Megaupload.com, a file-sharing site that allegedly facilitates Internet piracy. Since then, the group has taken credit for numerous other attacks on corporate and government websites.
But the charges in the PayPal case had one noticeable impact on the hacker group -- its members became more careful. They began circulating manuals online on how to use virtual private networks, or VPNs, to shield their IP addresses from the watchful eye of law enforcement, said Gabriella Coleman, a professor at McGill University who has studied Anonymous. "The arrests led to a kind of moment of education," she said.
The case against Covelli and the 13 other defendants stems from a series of cyberattacks in December 2010. In response to PayPal's decision to cut off donations to the whistleblower site Wikileaks, Anonymous encouraged supporters to download software that bombards websites with traffic, causing them to crash. The resulting "denial of service attack," which brought down PayPal's site intermittently over four days, was nicknamed "Operation Avenge Assange" in reference to the Wikileaks founder.
On Jan. 27, 2011, the FBI executed 27 search warrants and seized more than 100 computers in 12 states in connection with the PayPal attack. That day, Covelli said he was awoken at 6 a.m. by FBI agents knocking at his door. "The FBI is here," he recalled telling his girlfriend at the time. He opened the door and "got a pistol put to my face," he said.
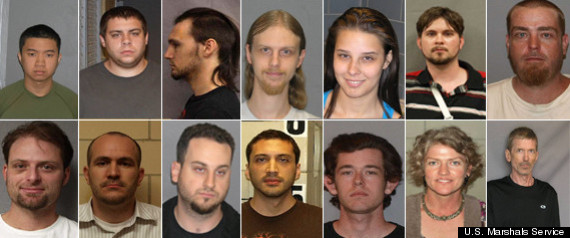
Six months later, authorities filed charges against 14 people, some of whom belie the stereotype of the teenage male hacker. The defendants are men and women ranging from 22 to 44 years old and living in small towns and big cities stretching from California to Florida. They include a real estate broker, a military veteran, a massage therapist and a single mother with two children.
Some knew each other before the indictment, but only by online nicknames such as "Anthrophobic" and "Reaper." They had never met in person until Sept. 1, 2011, when they made their initial court appearance together.
One defendant, Tracy Ann Valenzuela, a single mother and massage therapist, told a local ABC station in 2011 that she got involved in the PayPal attack while reading the news online.
"I saw something about PayPal shutting down payments to Wikileaks, and I clicked on some other site and joined a protest," she said. "And next thing I knew, my house was surrounded by guns."
Although 14 people were charged, PayPal collected about 1,000 IP addresses of computers involved in the attack, according to an FBI affidavit. Some observers have questioned whether those arrested in the case were high-level members of Anonymous or merely unsophisticated activists who wanted to be associated with the group and were unaware of the consequences of their actions.
"There were a handful who were core participants and a handful who were there because they were outraged that day and didn't know the consequences," said Coleman, the McGill professor.
She said the nature of the PayPal attack made it seem innocent to the untrained eye. "They were just sitting there firing requests with a piece of software from their computers," she said. "It doesn't feel all that criminal. It doesn't feel like you're causing harm."
But Mark Rasch, a former federal cybercrime prosecutor, said the Anonymous attack on PayPal should be considered a serious crime. He compared it to chaining a lock to the entrance of a store to prevent customers from entering. "If you do something illegal, the essence of civil disobedience is you run the risk of arrest and prosecution," he said.
Still, Rasch said the 14 PayPal defendants should be considered individually. "You need to look at the nature of their participation. Were they leaders or not?" he said. "It may be appropriate for some of these people to not be prosecuted or be given probation."
In interviews with The Huffington Post, defendants in the PayPal case said they have spent the past two years burdened by pre-trial conditions that restricted their Internet usage. Many also struggled to secure employment.
"When you're applying for a job and someone Googles you, you have a lot of explaining to do when you want to point out that you were standing up for free speech and a worthy cause and the government says you're a cyber terrorist," said Graham E. Archer, an attorney who represents Ethan Miles, one of the defendants.
Archer said being on pre-trial release has been "extraordinarily stressful" for Miles. Court records note that he spent time at a mental health facility.
"You have a pre-trial services officer who is in your life constantly," Archer said. "It's a form of out-of-custody incarceration for a lot of people."
Covelli, who went by the online aliases "Absolem" and "Toxic," said a brief stretch in which he was barred from using the Internet was "like a muzzle." A court-appointed officer routinely inspects his computer to ensure he is complying with pre-trial conditions that bar him from Internet chat rooms and knowingly communicating with other members of Anonymous.
Covelli said he has gone through various periods over the past two years during which "everything seemed dark and dim." He has been diagnosed with depression that is "exacerbated by the threat of prison that hangs over him," his attorney said in court filings.
"At first it was soul-crushing," Covelli told The Huffington Post. "I was like, 'Holy crap, everything is going to end. What am I going to do?'"
Today, Covelli is unemployed, living with his parents and volunteering 35 hours a week at a food pantry in Sidney, Ohio. He attended a drug treatment facility after violating pre-trial conditions by smoking marijuana, according to court records.
He now faces potentially 30 years in prison -- much longer than his co-defendants -- because he also has been charged in connection with a separate hacking case. Authorities say Covelli helped bring down Santa Cruz County's website in December 2010 in protest of a local ordinance that barred people from sleeping outdoors.
Covelli said his only possessions are a laptop and an Xbox that he received as a gift. The U.S. Marshall's Service pays for his flights to court hearings because his attorney has told the court that Covelli is indigent. "I ran out of money fast and have been living on almost nothing or from the generosity of my family," he said in an interview.
He found some work painting in Ohio but said he missed out on other job opportunities because of the charges against him. He briefly worked at a McDonald's restaurant, a gig he called "the best job I've had in two years." He lost one job because he was forced to request time off to attend a court hearing, his attorney said in court filings.
On Monday, Covelli tweeted from court that he was "bored" and suggested that supporters organize a game of whiffle ball outside the courthouse.
Another defendant in the PayPal case, Mercedes Renee Haefer, a 22-year-old sociology major at the University of Nevada-Las Vegas, told The Huffington Post that after the indictment was made public, one of her professors barred her from using her laptop in class, citing security concerns.
She said she didn't speak to her sister or father for several months and was fired from her job at a Sony retail store because of the charges. She said she has been unable to find jobs beyond part-time paralegal work for her lawyer and IT work for nonprofits. "No one will hire me," she said.
Haefer, a brunette who wears glasses and used the online aliases "No" and "MMMM," said she still believes in Anonymous, especially when the hacker group organizes attacks in defense of freedom of speech or freedom of information. "Some things they do I agree with and some things they do I don't agree with," she said.
She spoke to The Huffington Post by phone while riding her bike in Las Vegas. When a reporter suggested that activity might not be safe, she replied, "Safety is for losers."
Haefer said the case has brought her a small measure of fame, including an appearance in a recent documentary about Anonymous. "The day my indictment went public my name trended on Twitter," she recalled.
Before Monday's court hearing, she used the social media service to write: "Really excited that people are coming out to support us for court on the 13th. Makes the whole thing a little less dehumanizing. #paypal14"
In an interview, Haefer declined to discuss the PayPal attack beyond saying, "I was speaking out about an issue I feel passionate about."
She said she tries not to think about the possibility of going to prison.
"If I wake up every day thinking about 15 years in prison, I'm not really going to live my life," she said. "You can't sit and wait on your hands for three years."







