The Iranian group defeated the very basic phenomenon of an iPhone Fingerprinting scanner which allows them to hack TouchID with multiple Fingerprints also on iOS 7_0_2 .
An Iranian group of iPhone Geeks managing the blog
i-Phone.ir defeated
the very basic phenomenon of an iPhone Fingerprinting scanner, which
allows them to unlock an iPhone device with multiple Fingerprints. The
news has been provided in exclusive by the colleagues at
The Hackers News security portal that were contacted by the Iranian group.
The new is embarrassing for Apple firm
that known for the reliability of its products and the care of security issues.
The new Apple‘s iPhone 5s was recently presented as a new device that
includes a powerful feature, a biometrics-based security system called “
Touch ID” that read the user’s fingerprint to unlock the phone.
“Fingerprint is one of the best passcodes in the world. It’s always with you, and no two are exactly alike,” according to the Apple’s website.
The feature was immediately criticized, many security experts and advocates consider it a violation of user’s
privacy, but the troubles were just
began. The
TouchId features were soon compromised, Germany Hackers of
Chaos Computer Club
demonstrated how they were able to deceive Apple’s security
feature into believing they’re someone they’re not, using a well-honed
technique for creating a latex copy of someone’s fingerprint.
The same fate befell the
popular iOS 7 just released, the
lockscreen
feature in reality was not properly working allowing an attacker with
physical access to the handset to make calls and access to the
user’s data. Too much for a company like Apple!
The company promptly proposed an upgrade for its popular
iOS 7, but while all the iPhone users are celebrating for the efficiency of
Appleanother tile strikes on their heads.
As remarked by THN post another interesting fact is that, Touch ID is
not only designed to scan the fingerprints of your fingers, it works
with various human body parts and appendages which are also not fingers.
The concept behind the hack proposed by the Iranian group (Bashir
Khoshnevis , Mohsen Lotfi , Shayan Khabazian and other members of
i-Phone.ir support team) is that “No two Fingerprints are exactly alike”.
In the following video a proof of concept provided to
The Hacker News in which the Group set up a mixed Fingerprint scan
of 5-6 people for an iPhone 5S handset that allowed all of them to unlock the device with their individual fingerprints.

The curious data is that Apple officially declared that
TouchID
technology will misread 1 finger every 50,000, this is because Touch ID
is designed to unlock the device with partial part of the scan, this
means that providing a merged
thumbscan of multiple users to the unlock settings of an iPhone it will be able to read at least some partial scan of an individual user.
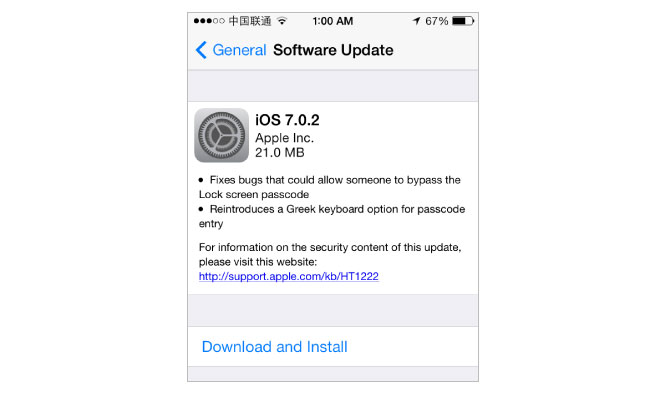
Does the newest
iOS 7_0_2 firmware fix the issue?
Apple released a couple of days ago the new
iOS 7_0_2 firmware release to fix the security issues discussed, but the hack proposed by the Iranian Team works also on the
iOS 7_0_2 as demonstrated by researchers at the THN ”
Wang Wie” and “
Jiten Jain“. The researchers tested the hack procedure on
iOS 7_0_2 firmware and it worked successfully.
Concluding, it is clear that Apple released too hastily the new patch for the security issues affected its new
iOS
7, it is curious that bugs like this last one works on a system just
patched. In the specific case it’s clear that Apple hasn’t implemented
properly biometric authentication …
meantime I suggest the use of old passcode to protect the
user’s device.