 Shubham Shah discovered a security flaw in the way Vodafone handled voicemail. Photo: Peter Rae
Shubham Shah discovered a security flaw in the way Vodafone handled voicemail. Photo: Peter Rae
The flaw was only resolved after Fairfax Media raised a series of questions about the vulnerability, which also exposed Vodafone customers to identity theft through unauthorised access to online services such as Google, which use two-factor authentication via a phone call.
The Vodafone flaw allowed anyone to "bruteforce" a target's voicemail PIN using easily accessible technology and gain access to the phone subscriber's voicemail messages.
 Huey Peard, 17, helped identify the flaw.
Huey Peard, 17, helped identify the flaw.The flaw also allowed outsiders to retrieve Vodafone customers' two-factor authentication codes, or tokens, used to access their Google, Yahoo and other online accounts.
These codes – which come in handy as a second layer of security when online log-in credentials are stolen – are usually sent via text message but can also be sent via a phone call and end up in voicemail.
In order to bypass two-factor authentication, hackers needed a user's online password, which security experts point out is relatively easy to retrieve these days with the high number of breaches occurring daily on the internet and password reuse. They also needed to engage the user's phone so that the code could be left in their voicemail.
There is no evidence to suggest hackers made use of the flaw on any of Vodafone's 4.9 million customer accounts. It was corrected in June but Fairfax waited until global carriers could secure their infrastructure before revealing it.
The researcher, Shubham Shah, is due to present his findings at the Ruxcon security conference in Melbourne next month alongside his friend and high school student Huey Peard, 17, one of the founding members of Gibson Security. Last year the group published exploits found in disappearing photo-sharing app Snapchat. The revelations allowed another group to release usernames and mobile numbers of 4.5 million Snapchat users online.
"We were made aware of research that identified a security issue with our visual voicemail service," Eyman Ahmed, head of information security at Vodafone, said in a statement. "Vodafone's technical team responded to the matter within a matter of hours, and has updated its systems to address it. We thank the researcher for responsibly disclosing this issue to us so that we could address it and ensure our customers remain protected."
But Mr Shah said the fix Vodafone implemented was not well thought out. It involved, he said, locking out hackers - as well as users - from their voicemail after five incorrect PIN attempts. This meant anyone could lock a user out, requiring them to call support to reset their voicemail PIN.
The vulnerability was linked to the carrier's visual voicemail offered to customers using Apple's iPhone. It's understood the four other global markets where Vodafone offers visual voicemail were not affected.
To notify others telcos about the flaw, Mr Shah informed the GSM Association (GSMA), a group whose members include global telecommunications companies.
James Moran of the GSMA said the group was "very grateful" for Mr Shah's co-operation and confirmed that operators were sent a security alert last week.
As the flaw potentially affects certain configurations of the visual voicemail system, Mr Shah also notified Apple, who acknowledged his findings.
"Thank you for contacting Apple Product Security," a company representative told him. "We appreciate you keeping us informed of your research, and hope your presentation goes well."
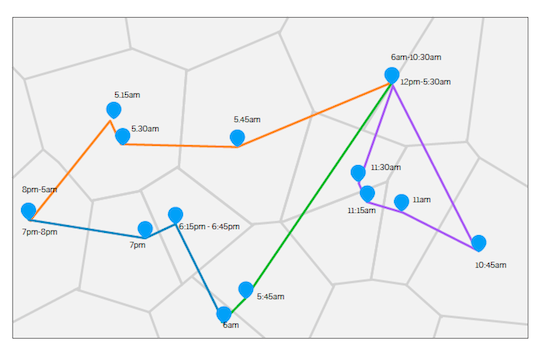 Splitting a user's trajectory can help preserve anonymity
Splitting a user's trajectory can help preserve anonymity
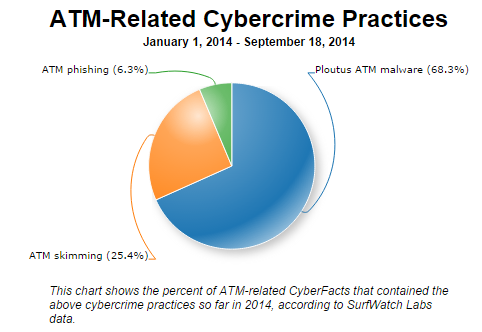 Using
malware to attack ATM machines is not a new technique being utilized by
hackers. When looking at ATM-related cybercrime practices this year,
Ploutus ATM malware is by far the most discussed.
Using
malware to attack ATM machines is not a new technique being utilized by
hackers. When looking at ATM-related cybercrime practices this year,
Ploutus ATM malware is by far the most discussed.