Summary: A man reportedly linked to Anonymous and a string of recent cyberattacks has been charged. 5 other suspects are in custody over the hacking of the official sites of Singapore's prime minister and president.
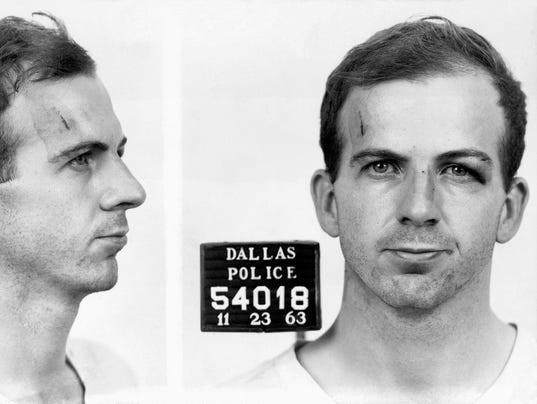
The man alleged to have hacked Singapore sites under the moniker "The Messiah" has been arrested by police, according to newsdaily Straits Times.Singapore police arrested James Raj Arokiasamy, 35, who was charged in court on Tuesday for hacking the site of Ang Mo Kio Town Council.
Raj is accused of hacking the town council's site from a unit in Dorchester Apartment at Jalan Sri Hartamas in Kuala Lumpur, Malaysia, on October 28 at about 1.35pm, according to Channel NewsAsia. He had allegedly defaced the site with an image of a Guy Fawkes mask and a message signing off as "The Messiah".
He is also suspected of hacking the sites belonging to The Straits Times, People's Action Party Community Foundation and City Harvest Church's co-founder and musician Sun Ho, according to a police statement.
He faces up to three years in jail and a S$10,000 (US$8,011) fine for one charge under the Computer Misuse and Cybersecurity Act. Separately, Raj also has been accused of three prior drug charges, which could add up to 10 years in jail and a S$20,000 (US$16,022) fine on each count.
According to Today. the prosecution asked that Raj be remanded in the Institute of Mental Health (IMH) for a psychiatric evaluation after he told the court that he was taking medication for Attention Deficit Hyperactivity Disorder (ADHD), had borderline personality disorder, suffered from depression, suicidal tendencies and hallucinations.
Raj was arrested by Malaysian police on November 4, and brought back to Singapore and charged for drug related offences the next day. The court then granted a one-week remand for further investigation.
How PMO site was "hacked"
According to Trend Micro, the attack was a result of typical Cross Site Scripting (XSS) where the cybercriminal exploited the "search" function on the site, and injected content from external sources. The cybercriminal had redirected the URL to the criminal's intended image. Exploited URL was then broadcast across various social networking sites implying that the PMO website has been defaced. With the exploited link referencing the official URL, unsuspecting visitors were tricked into thinking that the exploited link was a real defaced-PMO website.
Other suspects rounded up for PMO, Istana attacks
Police also have in custody five suspects who are assisting in investigations into the hacking of Prime Minister's Office (PMO) and Istana websites, according to the Straits Times. It added three suspects in the incident related to the hacking of the PMO site were family members. The other two suspects in the incident involving the presidential Istana site were Facebook friends. The men were aged between 17 and 45, added the article.The three hacking incidents currently appear to be unrelated, police said in its statement.
Last week, the PMO and Istana sites were defaced a day after Singapore Prime Minister Lee Hsien Loong pledged to "spare no effort" to "track down" hackers who targeted Singapore's IT infrastructure. He was responding to earlier threats by a hacker called "The Messiah", who claimed to be part of the Anonymous group and posted a YouTube video in protest of the Singapore government's online media licensing rule.