Kids walking around in goblin and vampire
costumes don't scare me on Halloween, nor do scary movies on TV. So what
is the scariest thing that happened so far today? It was a
phone call.
According to the Caller ID, this was a local number. When we
answered, a male voice identified himself as calling from the "Kings
County Sheriff's Office" and asked for a member of my family. When we
explained she wasn't available, we were told that there was an
outstanding warrant out for my family member. We were also told this
family member was going to be arrested in the next 45 minutes, because
of outstanding federal taxes from 2010.
We are always willing to cooperate, within reason, so we asked for
more information. After giving us a a phone number and the name of the
person we should speak with at the federal government office, the caller
transferred us to that number. The federal agent who answered the phone
claimed if we wanted to resolve this right away, we would have to
provide a cell phone number. The person wasn't very pleased when we
refused, and kept repeating that our lack of cooperation meant this
family member would be arrested in 45 minutes.
Scary? A little bit.
Red Flags AplentyLong-time readers of
SecurityWatch
would have noticed right away some of the red flags indicating that
this was a scam, and not a real call. Let's walk through them.
1. New York City residents know that we don't have a "Kings County
Sheriffs Office." We have the NYPD. However, we do actually have a
Sheriff's Office,
though, and it does handle tax evasion issues, but as the friendly
spokesperson at the Sheriff's Office told me today, the office doesn't
do anything with the federal government. The Sheriff's Office handles
only cases for local taxes, and even that isn't a big part of their
normal caseload, he said.
2. The caller kept saying "federal government"—not the IRS. Not the Internal Revenue Service. Try again, buddy.
3. Law enforcement doesn't call and say "pay up or we will arrest you." Not only would they
not
call me at home first, but they also won't give me the opportunity to
make this go away first. As my new buddy at the Sheriff's Office said,
"That's not how the system works." If there really was a warrant, the
arrest would happen first, and then there will be the opportunity to fix
it. Usually with a judge.
4. The time pressure to "act in 45 minutes" was clearly a social
engineering tactic to create a high-pressure situation, said White Hat
Security's Robert Hansen. This is a little similar to the kind of
ransomware and
scareware
scams we've talked about in the past, where they create a sense of
urgency, and if we don't take action right away, something bad will
happen. In the cases of
CryptoLocker and other
types of ransomware, the
malware might actually carry out on the threat.
5. I didn't mention this in the above summary, but we were told we
were going to be transferred to speak with "Michael Black." Yet when he
answered, he said, "This is Khan." When we asked for Michael Black, he
said, "It's the same."
You know, if you are going to run a scam operation, get your names straight.
When I mentioned to the Sheriff's Office spokesperson the caller
claimed the amount due was $1,798, he laughed and said, "There are
people who owe tons more than that and don't get arrested."
Remember, if there really was an issue of overdue taxes, the IRS, or
any government entity for any kind of problem really, would first send a
letter by postal mail. And follow up by mail. The initial call wouldn't
come from law enforcement.
"You don't get an arrest warrant. You just get a lot of mail," Chester Wisniewski of Sophos told me.
The scammers wanted us to act quickly, and were mad we didn't. They
kept mentioning how it would be our fault if the arrest happened. In
this case, and I really hope I am right, it's unlikely an arrest will
happen any time soon.
Don't Panic. Think.It
helped that we didn't panic and fall into the trap of thinking we had to
do something right away, because we were able to detect other flags.
"Probably the best way to react is to relax first," Hansen recommended.
We demanded information. They didn't have much, and kept insisting on
a cell phone number. Eventually they asked for an email address.
Haven't seen anything in my inbox yet, but as soon as it arrives, rest
assured I will be sending it to trusted experts to find out what it has.
"Don't trust anything that is coming to you that you don't know where
it is coming from," Wisniewski said. "Hang up, and call back the bank,
the government, whoever the person is, and verify this is real." If
this was a legitimate employee from a company, or a member of law
enforcement, they will immediately provide the necessary information,
such as the name, extension, and badge number, so that you can verify
who they are.
The same rule applies if this happened over email instead of a phone
call. Don't click on the link, but go directly to the organization site
and see if you can get more details.
We immediately called the IRS—not with the number the caller gave us, but by looking it up on
IRS.gov—and
also the Sheriff's Office. In fact, when we called the Sheriff's
Office, the spokesperson immediately said that we weren't the first ones
reporting this scam.
You should also try to gather as much information as possible on the
person calling so that you can report it to the real law enforcement.
We got the person's "name"—both the first name and last name—and the
phone number. We were unable to get more details, such as their title,
their badge number, the department they work at, the docket number/case
number they are working from, etc.
"Trust your gut. If the call doesn't seem right, trust that feeling,"
Wisniewski said. He also noted that in these situations, hearing an
Indian accent generally puts him on guard because of past scams (such as
the Microsoft support scam) originating from Indian call centers. I am
not saying all Indian accents are suspect (my entire family has an
accent), or that non-accented callers are always legitimate. But
consider that there have been a lot of suspicious calls recently and it
is one thing to consider if you are feeling suspicious.
What Was the End Game?I described the whole scam
to Wisniewski and he was intrigued, saying this sounded like a new type
of scam. I am curious as to what the end game was. Was the cell phone
number so that they could SMS me a link to the payment portal? Why
didn't they ask for a credit card number?
This could have been an attempt to sign me up to a premium-rate
number where I would get billed for services such as Joke-of-the-Day,
but it seems like the caller was taking a lot of risks with this
approach, noted Wisniewski. This could have been an attempt to send out
SMS spam, as well.
It's possible they were originally trying to reach my family member
directly to get identifiable information such as social security number
and credit card information, suggested NetIQ's Geoff Webb. Since the
person didn't answer the phone, they then switched to "cramming" me,
where they would append fake charges to the cell phone bill, Webb
speculated.







 The proxy (
The proxy (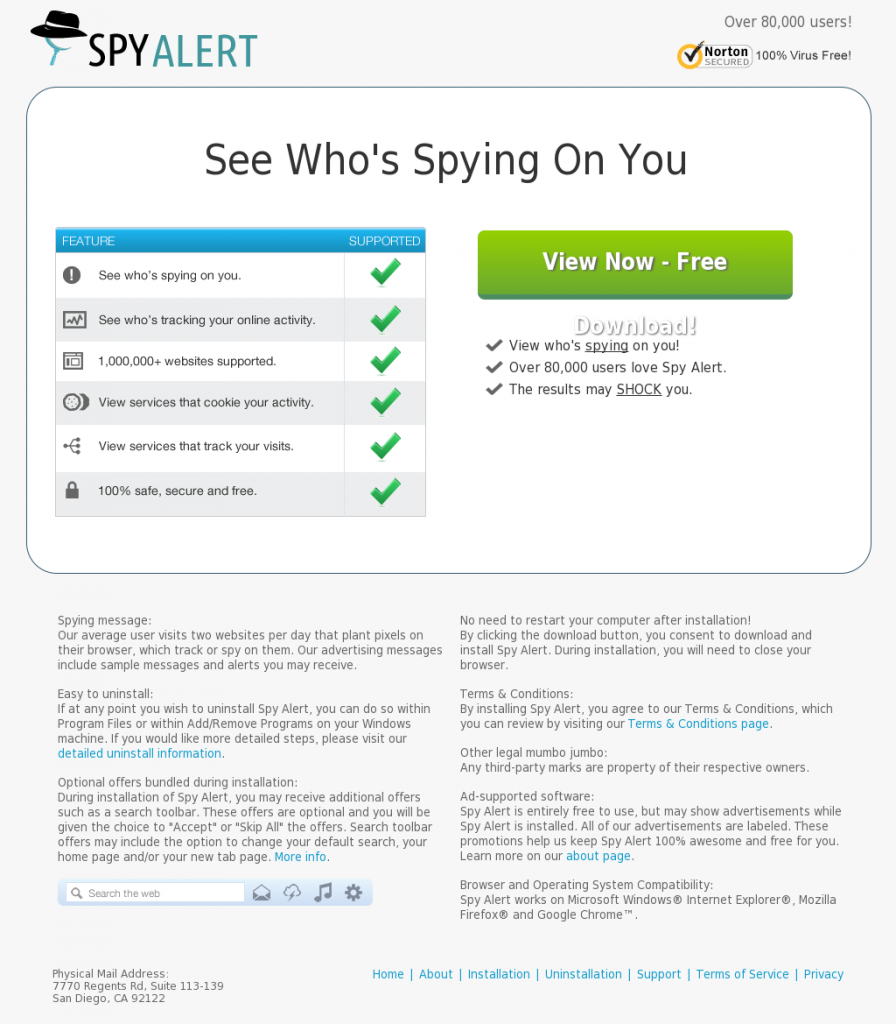 Landing URL: spyalertapp.com
Landing URL: spyalertapp.com