The Federal Bureau of Investigations has released a formerly in-house
malware-analysing portal to help speed up incident responses and help
industry and law enforcement with investigations.
The G-men hope the
Malware Investigator portal can let businesses build responses to new malware without such heavy reverse-engineering loads.
Information crime unit chief Steve Pandelides said during the
portal's initial launch it would benefit the agency and the private
sector.
"After submission, the report can get turned around in a matter of minutes to a matter of hours," Pandelides said.
"It
will enable our private partners to protect their company's networks
and help our state and local law enforcement partners further their
investigations.
"It will also provide the FBI a global view of the malware threat."
Malware Investigator: FBI
Windows malware submitted to the portal would be correlated
against other submissions and the FBI's intelligence to produce reports.
It would be expanded to cater for other virus types.
Malware
would be analysed in part through fuzzy hashing including section
hashing, virus scanning cluster, sandboxing, file system modification
and others.
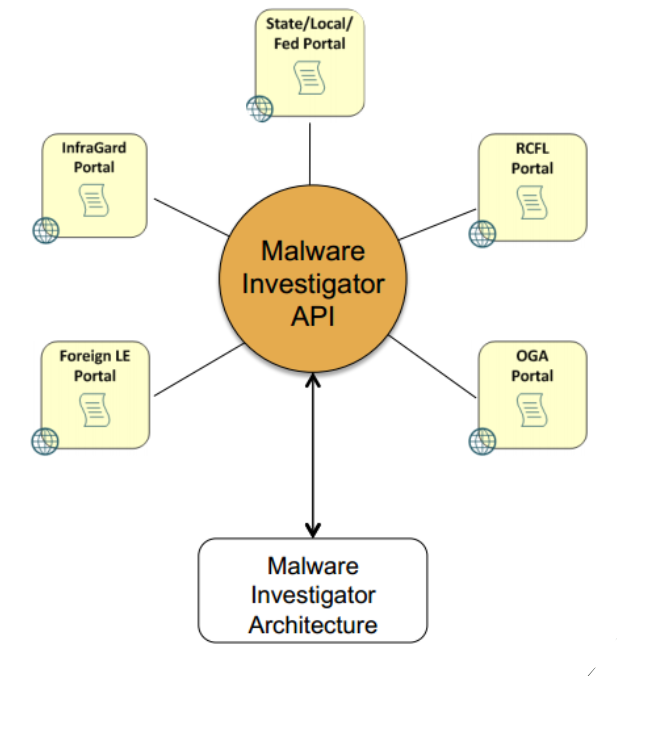
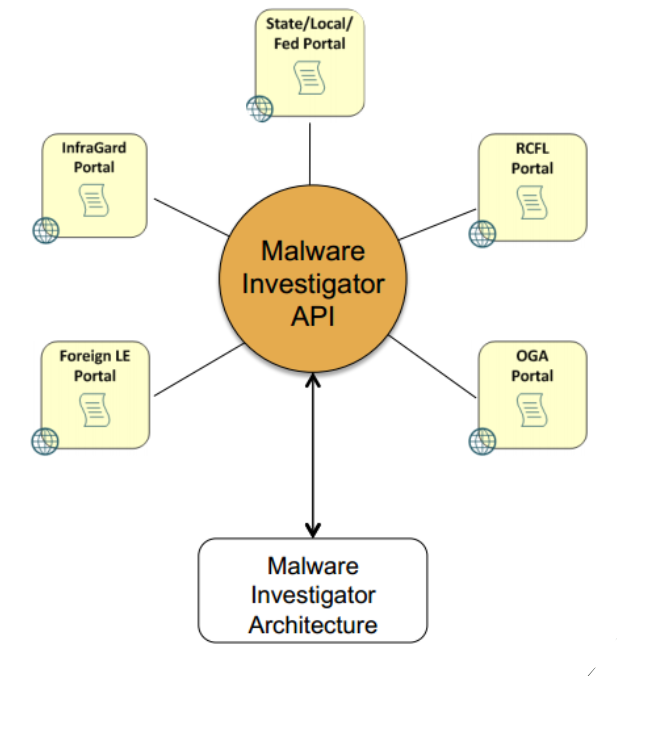
The agency opened API access for organisations seeking
to integrate the system into their platforms, and maintained that a
submitters' private details would remain undisclosed, the Bureau's
Jonathan Burns said at the
Virus Bulletin conference in Seattle last week.
The
FBI began manual malware analysis in 1998 and over subsequent years had
built systems to help store and examine viruses, trojans, worms and
bots. The process became automated in 2011 with work beginning on
Malware Investigator last year.