When Mike Tigas first created the Onion Browser app for iOS in 2012, he never expected it to become popular. He was working as a newsroom Web developer at The Spokesman-Review in Spokane, Washington, at the time, and wanted a Tor browser app for himself and his colleagues. Expecting little interest, he then put Onion Browser on the Apple App Store at just $0.99/£0.69, the lowest non-zero price that Apple allows.
Fast forward to 2016, and Tigas found himself living in New York City, working as a developer and investigative journalist at ProPublica, while earning upwards of $2,000 a month from the app—and worrying that charging for it was keeping anonymous browsing out of the hands of people who needed it.
So a few weeks ago, he made the app free. Since then, its popularity has exploded, with thousands of downloads recorded every day. The results of the recent US presidential election might have had something to do with this decision, and its impressive results, Tigas told Ars. "Given recent events, many believe it's more important than ever to exercise and support freedom of speech, privacy rights, and digital security," he wrote in a blog post. "I think now is as good a time as ever to make Onion Browser more accessible to everyone."
Global concerns also influenced his decision. "Iran is not technically a country where you can get an iPhone, but on the grey market you can," he told Ars. "People over there can't get apps you have to pay for, because you have to have a credit card that Apple actually accepts," he added, noting that economic sanctions forbid Apple from selling to Iranian iOS users.
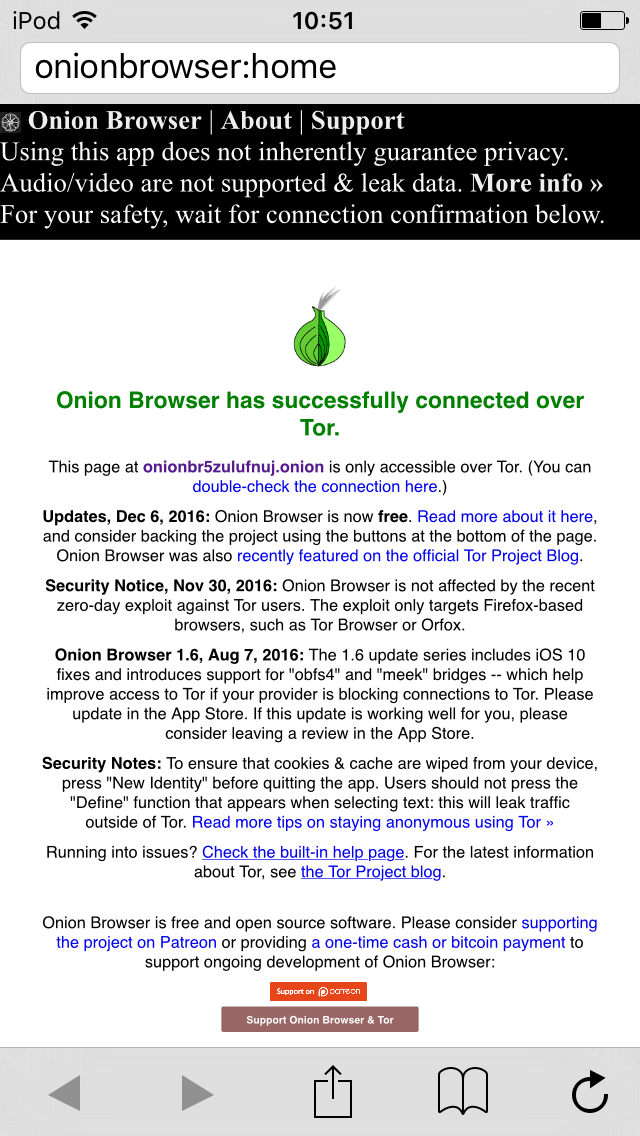
Onion Browser is the official Tor Project-endorsed Web browser for iOS. But it lacks some of the features available for Tor Browser (Linux, MacOS, Windows) and OrFox (Android), due to technical roadblocks peculiar to iOS.
Developers have found workarounds to both problems, and iOS users can soon expect to see a new, improved Onion Browser, as well as a Tor VPN that routes all device traffic over Tor—probably in the first quarter of 2017.
Not quite as secure
Unlike the Tor or OrFox, Onion Browser is not based on the Firefox Gecko rendering engine. This is good—Onion Browser is not vulnerable to Firefox exploits—but also bad, because code cannot be reused.A further challenge, Tigas said, is that Apple’s WebKit APIs "don’t allow a lot of control over the rendering and execution of Web pages, making a Tor Browser-style security slider very difficult to implement."
Many of iOS's multimedia features don't use the browser's network stack, making it difficult to ensure the native video player does not leak traffic outside of Tor.
"Onion Browser tries to provide some functionality to block JavaScript and multimedia, but these features aren’t yet as robust as on other platforms," Tigas wrote.
Moreover, it doesn't support tabbed browsing, and the UX is pretty basic, but Tigas is working on a rewrite based on Endless. "It adds a lot of important features over the existing Onion Browser,” he said, “like a nicer user-interface with tabbed browsing, HTTPS Everywhere, and HSTS Preloading. There’s a new version of Onion Browser in the works that’s based on Endless that will hopefully enter beta testing this month."
Welcome to the sandbox
The biggest challenge to getting Tor working seamlessly on iOS, though, is the inability to run Tor as a system-wide service or daemon, something which is trivial to accomplish with most other operating systems, but unavailable to iOS app developers. To prevent misbehaving apps from getting up to their usual mischief, Apple sandboxes apps from each other, and from the underlying OS. This means you can't install Tor on iOS, let it run in the background, and route all your device traffic over Tor.“In iOS the moment you leave an app, the app goes to sleep,” Tigas told Ars. “With Tor Browser Bundle or OrBot on Android, other apps can use the Tor in Tor Browser Bundle, other apps can use OrBot's connection on Android.”
In fact, to get Onion Browser to work, he has to compile Tor into the app itself—as does any other iOS app developer who wishes to offer a Tor connection. But that's about to change, thanks to iCepa.
A Tor VPN for iOS
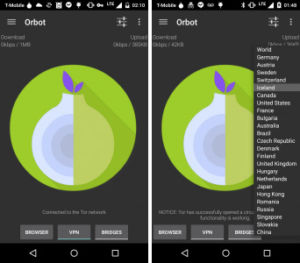
Enlarge / OrBot, the official Tor routing service for Android.
"It's similar to how OrBot works," he added, "which also uses a VPN approach."
Apple-imposed memory limits had prevented Kramer from finishing work on iCepa until recently. The memory limit for packet-tunnel extensions, he explained, was 5MB—and Tor needs around 10MB to run.
Kramer said he was able to continue development work on a jailbroken iOS 9 device, but with little motivation since a jailbroken solution would not scale. An encounter with Apple engineers at the WWDC conference gave him the chance to lobby Apple engineers to raise the limit—which they did, in iOS 10, to 15MB, more than enough to get a Tor VPN working in iOS.
Kramer told Ars he had just gotten iCepa working on his test device in mid-December, and plans to share the working code in a private alpha with other Tor developers before the end of the year. He hopes to release iCepa to the public through the App Store at the end of the first quarter of 2017.
"The timeline is still uncertain," he emphasised, "but I do want to get it out as soon as possible.”
Paying for Tor development
Since making Onion Browser free in early December, Tigas says the number of downloads has jumped from around 3,000 paid downloads per month to thousands per day. He is at peace with his decision, though, convinced he has done the right thing, but worries about the loss of income."[The extra money] helped keep me doing investigative journalism by day," he told Ars. "If I can get to even 15 percent of where it was before, I would be really happy and amazed. I think I have like five people on Patreon right now."
Tigas has received some financial support from the Guardian Project to continue work on Onion Browser, but, he says, the money does not come close to replacing the income lost from the App Store.
“I'm still a little terrified that I've made this change,” he wrote in his blog post, “but I'm happy this day has come—and judging from the responses I've already received, so have many of you. Thanks for your support.”

