Dan Goodin, Ars Technica
Most of the existing corpus of passwords exposed in hack attacks is stripped of usernames, preventing researchers from studying the possible relationship between the two fields. Mark Burnett, a well-known security consultant who has developed a specialty collecting and researching passwords leaked online, said his sole motivation for releasing the data was to advance what's already known about the way people choose passcodes. At the same time, he said he was worried the list might land him in legal hot water given the recent five-year sentence handed to former Anonymous activist and writer Barrett Brown, in part based on links to hacked authentication data he posted in Internet chat channels.
"I think this is completely absurd that I have to write an entire article justifying the release of this data out of fear of prosecution or legal harassment," he wrote in a post published Monday night on his blog. "I had wanted to write an article about the data itself but I will have to do that later because I had to write this lame thing trying to convince the FBI not to raid me."
Last March, federal prosecutors dropped criminal charges related to links Brown left in two Internet relay chat channels that were frequented by members of the Anonymous hacker collective. The links led to authentication data taken during the December 2011 hack on Strategic Forecasting by members of Anonymous. Before dropping the charge, prosecutors said the links amounted to the transfer of stolen information. Even though the charge was dropped, however, prosecutors still raised the linking to support their argument Brown deserved a long prison sentence.
In Monday night's post, Burnett also raised changes the Obama administration is proposing to federal anti-hacking statutes. Many security professionals have said the revised law would outlaw the publication of links to public password dumps even if the person making the link had no intent to defraud. If the people sharing the information have any reason to believe someone might use it to gain unauthorized computer access, critics have argued, they would be subject to stiff legal penalties under the Computer Fraud and Abuse Act.
Burnett wrote:
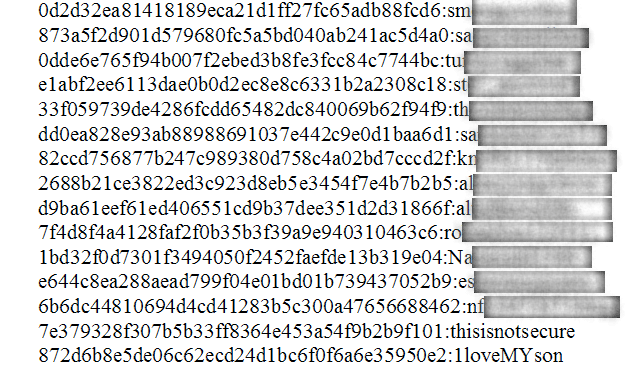
But recent events have made me question the prudence of releasing this information, even for research purposes. The arrest and aggressive prosecution of Barrett Brown had a marked chilling effect on both journalists and security researchers. Suddenly even linking to data was an excuse to get raided by the FBI and potentially face serious charges. Even more concerning is that Brown linked to data that was already public and others had already linked to.Including usernames alongside passwords could help advance what's known about passwords in important ways. Researchers, for instance, could use the data to determine how often users include all or part of their usernames in their passwords. Besides citing the benefit to researchers, Burnett also defended the move by noting that most of the leaked passwords were "dead," meaning they had been changed already, and that all of the data was already available online.
In 2011 and 2012 news stories about Anonymous, Wikileaks, LulzSec, and other groups were daily increasing and the FBI was looking more and more incompetent to the public. With these groups becoming more bold and boastful and pressure on the FBI building, it wasn’t too surprising to see Brown arrested. He was close to Anonymous and was in fact their spokesman. The FBI took advantage of him linking to a data dump to initiate charges of identity theft and trafficking of authentication features. Most of us expected that those charges would be dropped and some were, although they still influenced his sentence.
At Brown’s sentencing, Judge Lindsay was quoted as saying “What took place is not going to chill any 1st Amendment expression by Journalists.” But he was so wrong. Brown’s arrest and prosecution had a substantial chilling effect on journalism. Some journalists have simply stopped reporting on hacks from fear of retribution and others who still do are forced to employ extraordinary measures to protect themselves from prosecution.
Which brings me back to these ten million passwords.
Why the FBI Shouldn’t Arrest Me
Although researchers typically only release passwords, I am releasing usernames with the passwords. Analysis of usernames with passwords is an area that has been greatly neglected and can provide as much insight as studying passwords alone. Most researchers are afraid to publish usernames and passwords together because combined they become an authentication feature. If simply linking to already released authentication features in a private IRC channel was considered trafficking, surely the FBI would consider releasing the actual data to the public a crime.
As password dumps go, 10 million is a large number, but it's still small compared to the seminal 2009 hack of gaming website RockYou, which leaked 32 million passcodes, 14.3 million of which were unique. Last year, The New York Times reported that Russian criminals amassed a database of more than one billion passwords gathered from more than 420,000 websites. As Burnett noted, what sets this latest dump apart is that it was made by a security professional with the goal of advancing the public understanding of password choices. Equally noteworthy will be the reaction it receives from prosecutors.
No comments:
Post a Comment